AI
AI
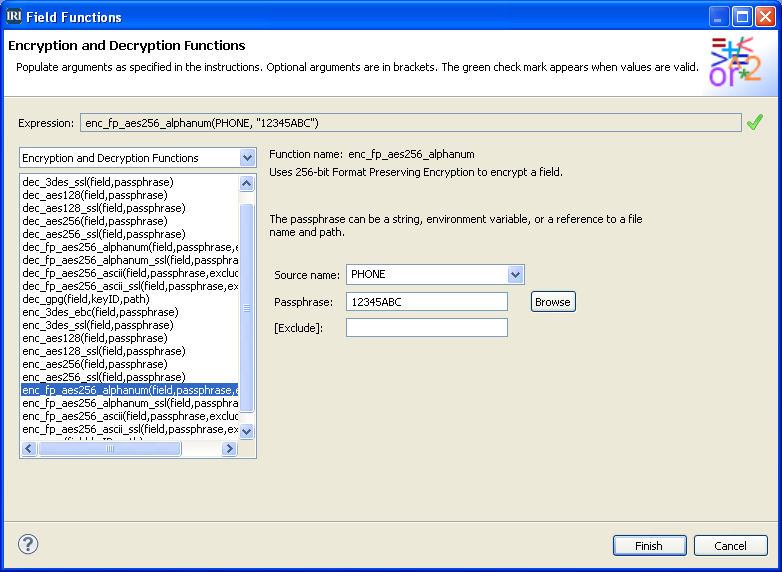
AI Data Classification for RDBs
IntroductionData Classification in the IRI Workbench GUI is used to name and find specific kinds of data – usually Personally Identifiable Information (PII) – and to consistently apply chosen functions (e.g., Read More