 Data Masking/Protection
Data Masking/Protection
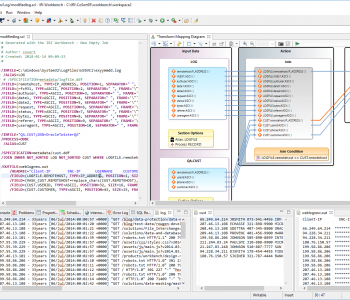
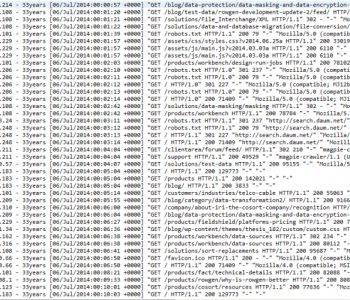
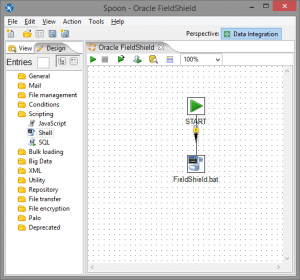
Masking Data in Pentaho
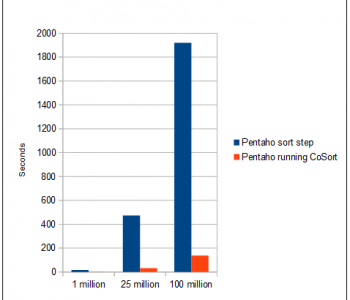
This article is second in a 3-part series on using IRI products to expand functionality and improve performance in Pentaho systems. We first demonstrate how to improve sorting performance, and then introduce ways to mask production data, and create test data, in the Pentaho Data Integration (PDI) environment. Read More