 Test Data
Test Data
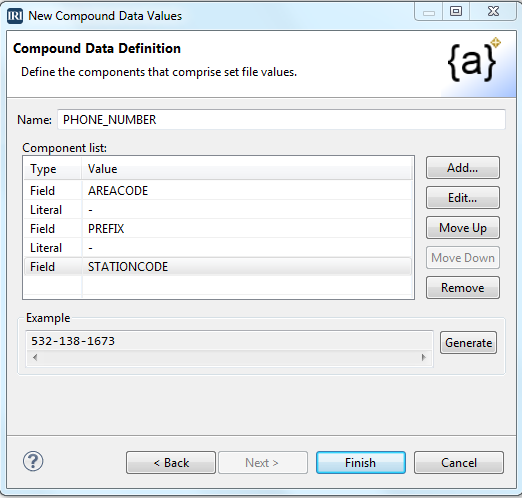
Test Phone Number Generation: Using RowGen’s Compound Data Value…
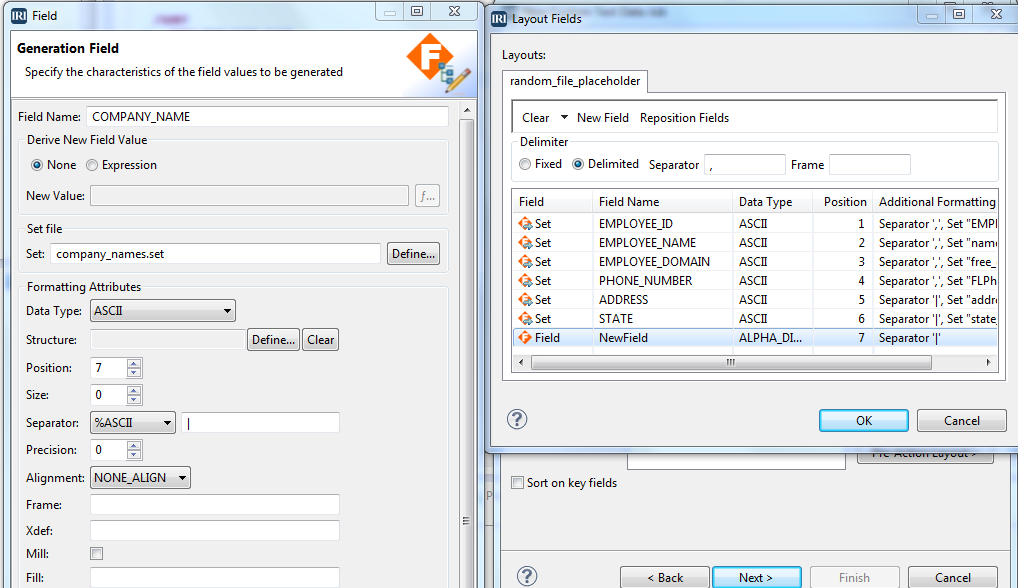
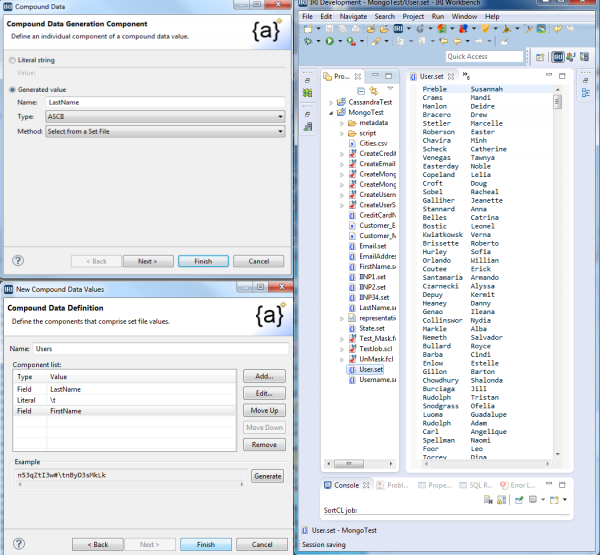
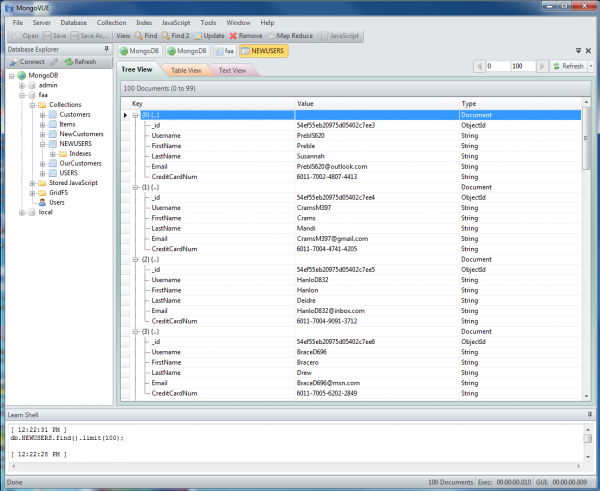
One of the ways IRI RowGen builds realistic test data is through the formation and population of custom field values, such as phone numbers. In this article, we explain how to use the Compound Data Value (CDV) wizard in the RowGen GUI to build a set file containing real-looking, US phone numbers based on the North American Numbering Plan (NANP). Read More