Securing FieldShield Encryption Keys with Alliance Key Manager
In a previous article, we detailed a method for securing the encryption keys (passphrases) used in IRI FieldShield data masking jobs through the Azure Key Vault. Read More
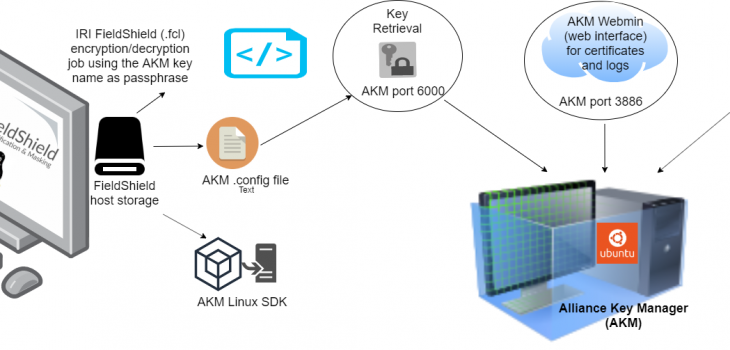
In a previous article, we detailed a method for securing the encryption keys (passphrases) used in IRI FieldShield data masking jobs through the Azure Key Vault. Read More
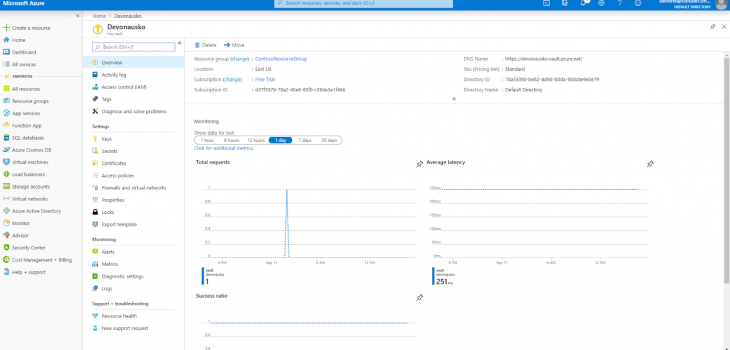
Abstract: This article covers Azure Key Vault encryption key management as part of data encryption best practices. It explains how to use Azure Key Vault and how to perform secure passphrase storage in Azure for encryption and decryption in the IRI FieldShield data masking tool. Read More
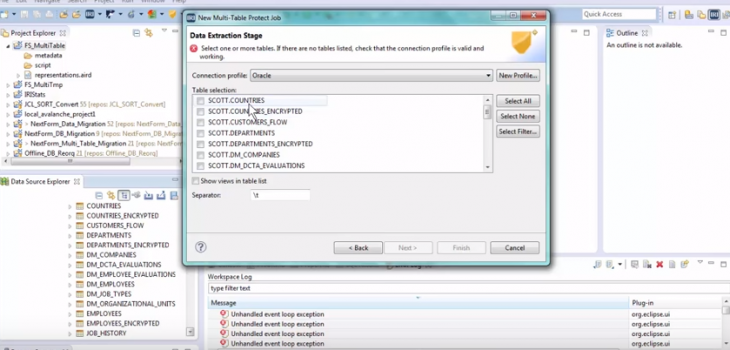
In this demonstration, the Multi-Table Protect Job Wizard in the IRI Workbench GUI for Fieldshield and Voracity is used to define a rule for data in multiple Oracle tables. Read More

Introduction: This example demonstrates an older method of using IRI FieldShield to protect sensitive data prior to indexing the data in Splunk. As you will read, FieldShield would process the data outside of Splunk and create a CSV file for Splunk’s ingestion. Read More
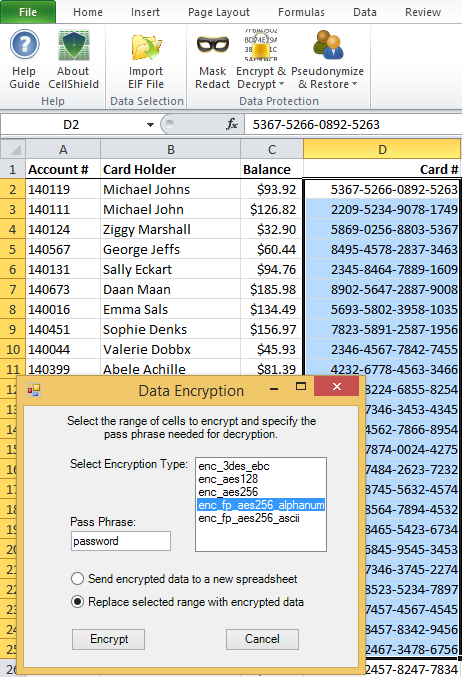
This is the third in a four-part series describing IRI CellShield data masking software for Excel, and its format-preserving encryption function in particular; the series overview starts here. Read More
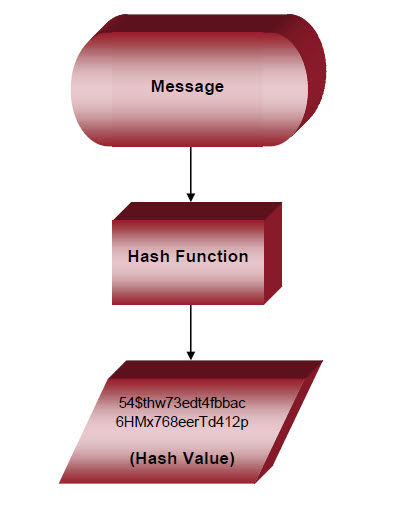
Hashing and encryption are distinct disciplines. Indeed, the differenced between hashing and encryption can be stark:
According to the SSL Store, “encryption is a two-way function where information is scrambled in such a way that it can be unscrambled later. Read More
According to Trent Henry of the Burton Group,
Data protection needs to take into account both internal and external threats, including those against critical database and application resources. Read More
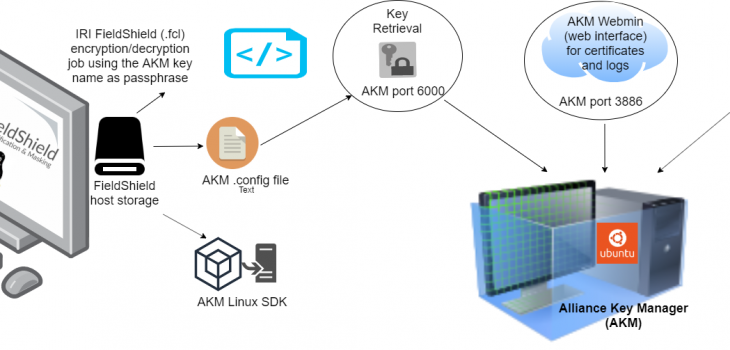
Encryption key management is one of the most important “basics” for an organization dealing with security and privacy protection. Major data losses and regulatory compliance requirements have prompted a dramatic increase in the use of encryption within corporate data centers. Read More

It is a common mistake to refer to data masking and data encryption interchangeably to mean the same things. While field-level encryption is considered one of many possible “data masking” functions, we define data masking and encryption as technically distinct processes below. Read More
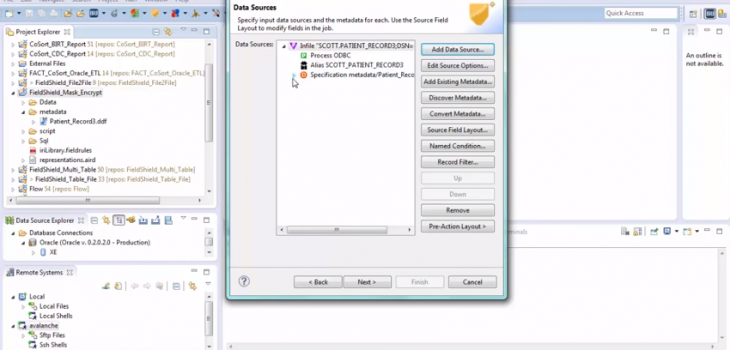
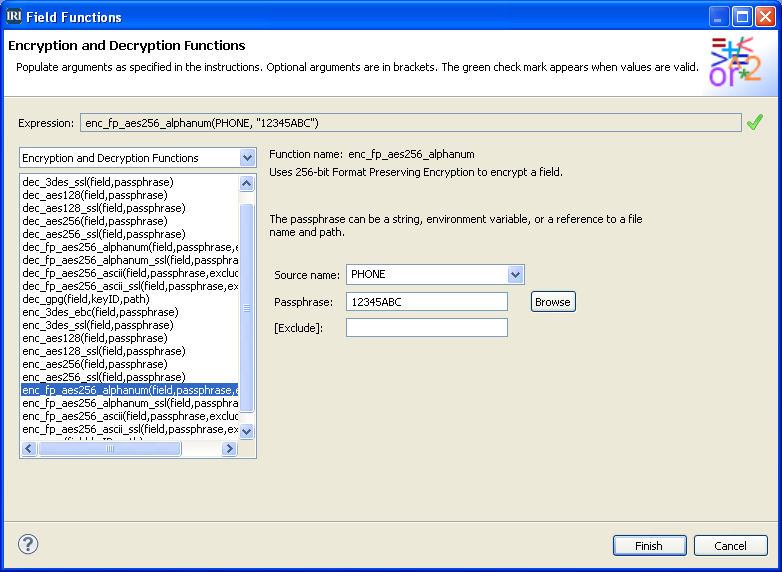
This demonstration shows how to use IRI FieldShield in Workbench to create a script to protect personally identifying information (PII) at the field level. Masking functions and encryption algorithms are applied to separate fields in a database in the same pass. Read More