Data Masking/Protection
Data Masking/Protection
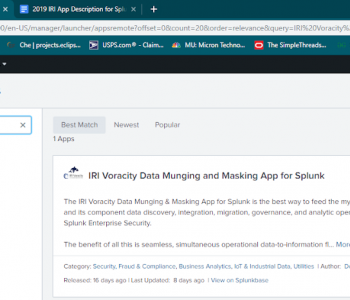
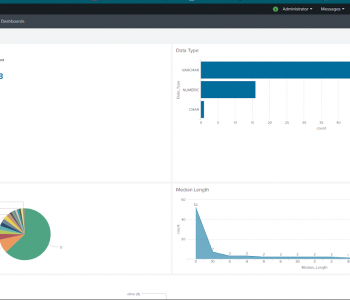
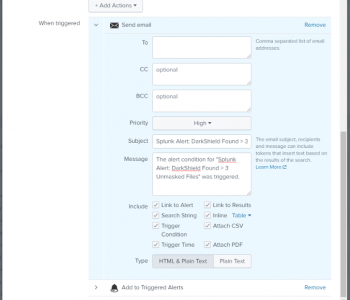
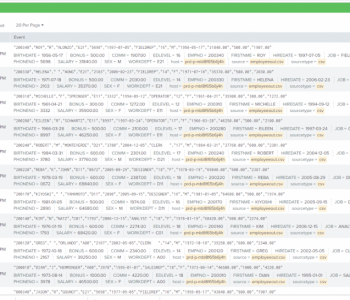
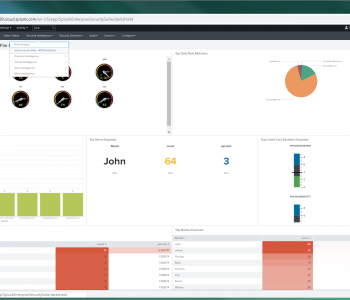
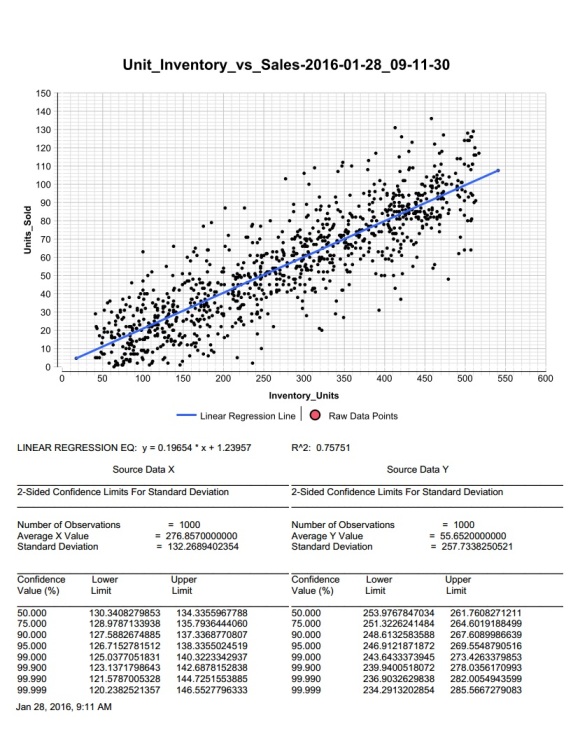
Masking PII in Splunk, Redis & CosmosDB
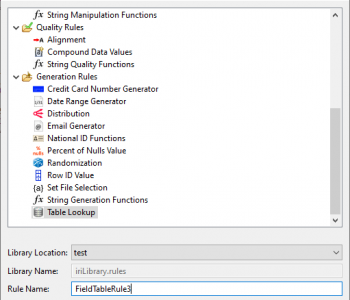
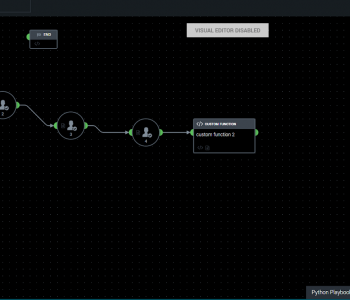
Editor’s NoteThis is the third article in a series of articles on using IRI DarkShield to search and mask sensitive data in NoSQL databases. IRI Workbench GUI for DarkShield currently supports the following NoSQL databases:
Cassandra Elasticsearch MongoDBFor detailed instructions on using the DarkShield wizard with these databases and their configuration requirements, refer to this article. Read More