Managing MarkLogic Data in IRI Voracity
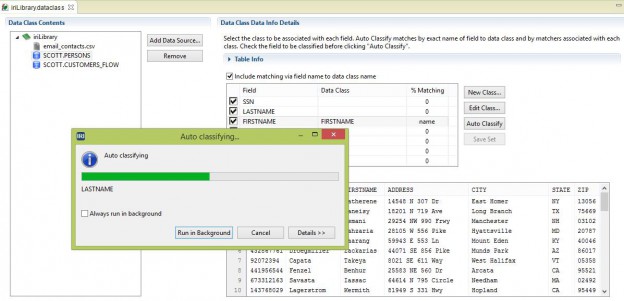
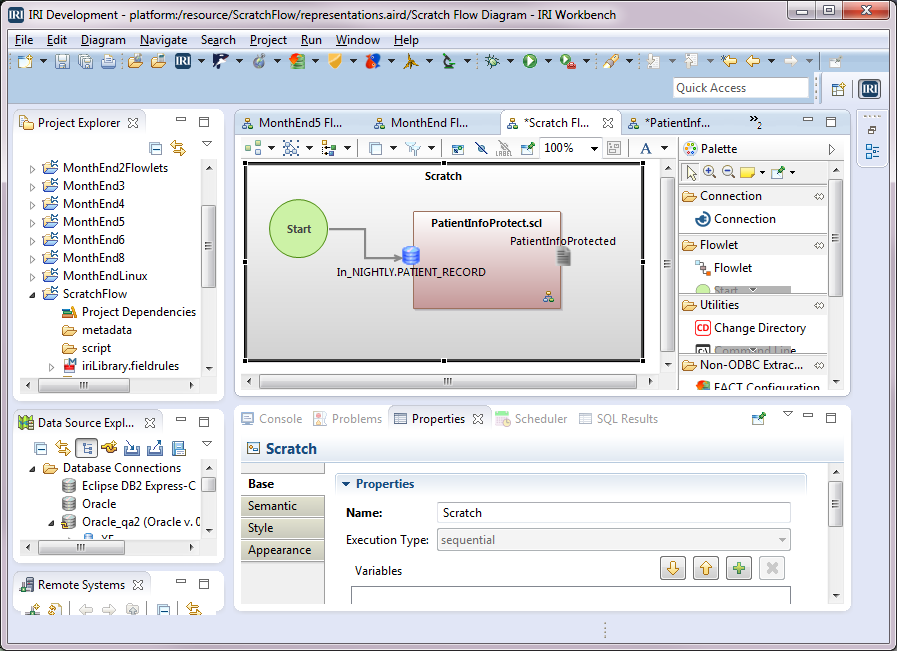
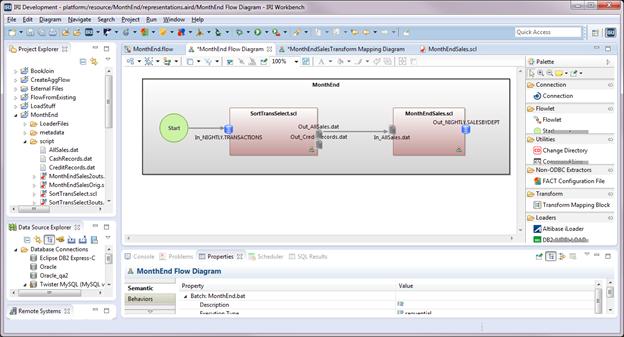
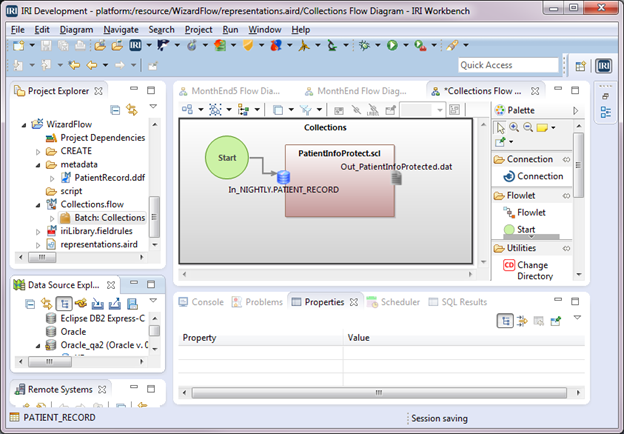
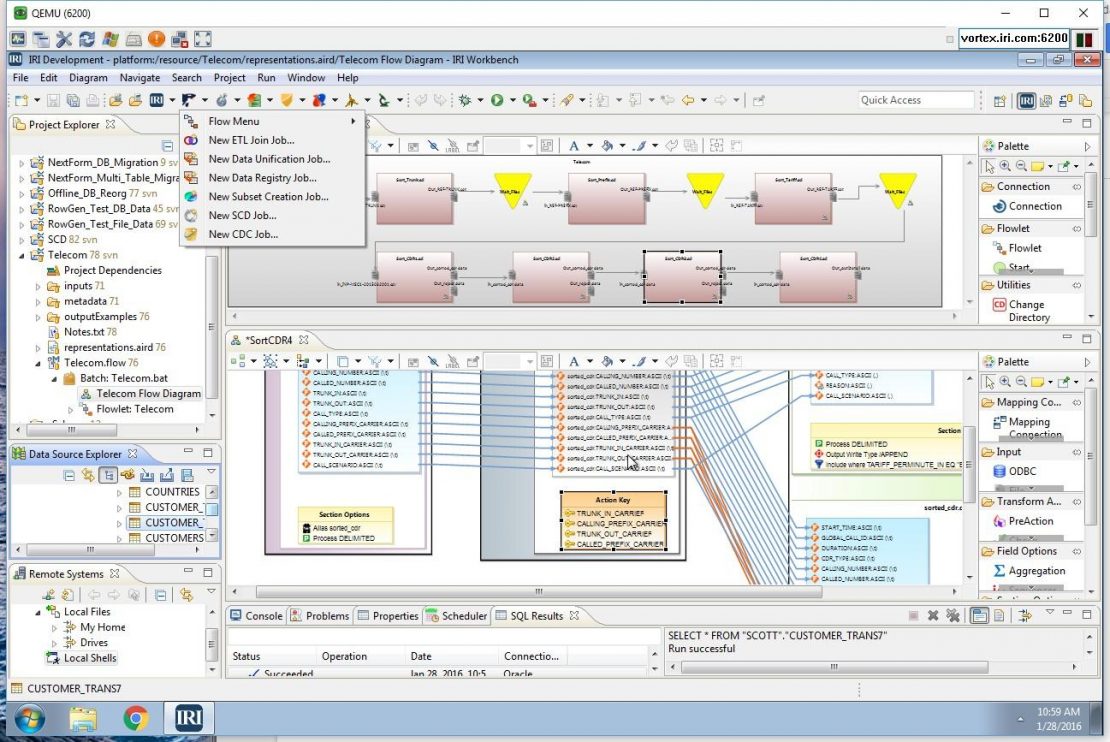
The IRI Voracity data management platform now supports the MarkLogic NoSQL database as a source for structured data discovery (classification, profiling, and search), integration (ETL, CDC, SCD), migration (conversion and replication , governance (data cleansing and masking), and analytic (reporting and wrangling) jobs. Read More