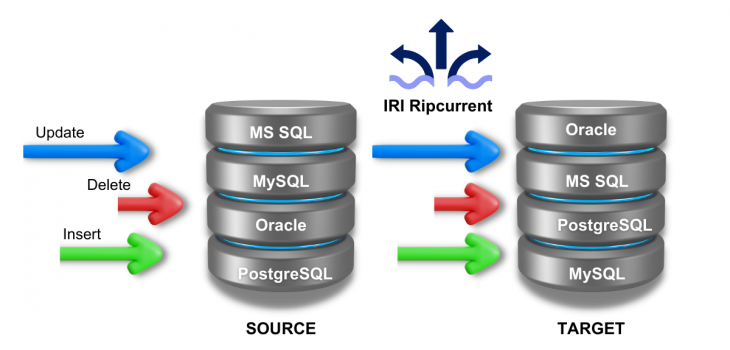
Real-Time Database Data Replication
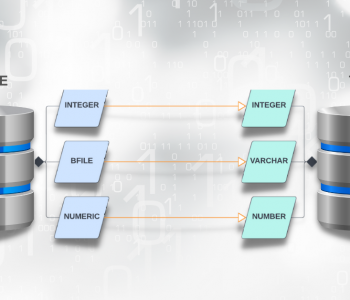
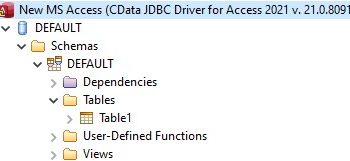
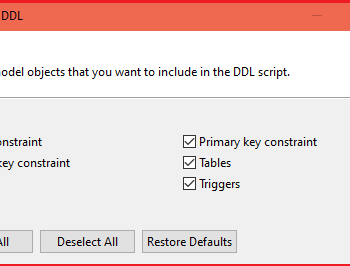
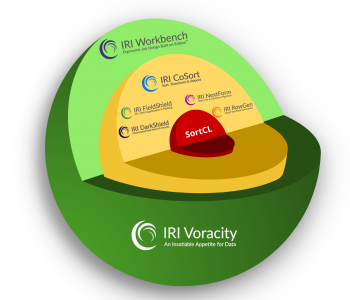
Abstract: The previous article in this series of 4 detailed how to install, set up, and configure IRI Ripcurrent, an IRI-developed command-line Java application that utilizes the Debezium embedded engine and the streaming feature of the IRI (CoSort) SortCL program to react in real-time to database change events by replicating data to downstream target(s), optionally with transformation (e.g., Read More