Static & Dynamic Data Masking in FieldShield
Usually static data masking is performed on production data at rest so it is stored safely, or when replicated to non-production environments for testing or development purposes. Dynamic data masking (DDM) is performed on data in production tables during queries, so that those not authorized to see original column values will see redacted views of the values in their application instead.
It’s well known that IRI FieldShield is a static data masking product. But it can also be used to mask and unmask data in databases and flat files in a more dynamic way. We have seen use cases requiring either, or both, when the data at risk are at rest (static) or in motion (dynamic) and need to be protected.
DDM via ‘redaction in flight’ is available from IRI through: API-callable masking libraries you can make on an authenticated, custom basis from C, C++, Java or .NET applications (see SDK here); SQL (procedure) calls; and soon, a special JDBC driver managed via proxy server. This article addresses the first method for dynamic unmasking in conjunction with static data masking.
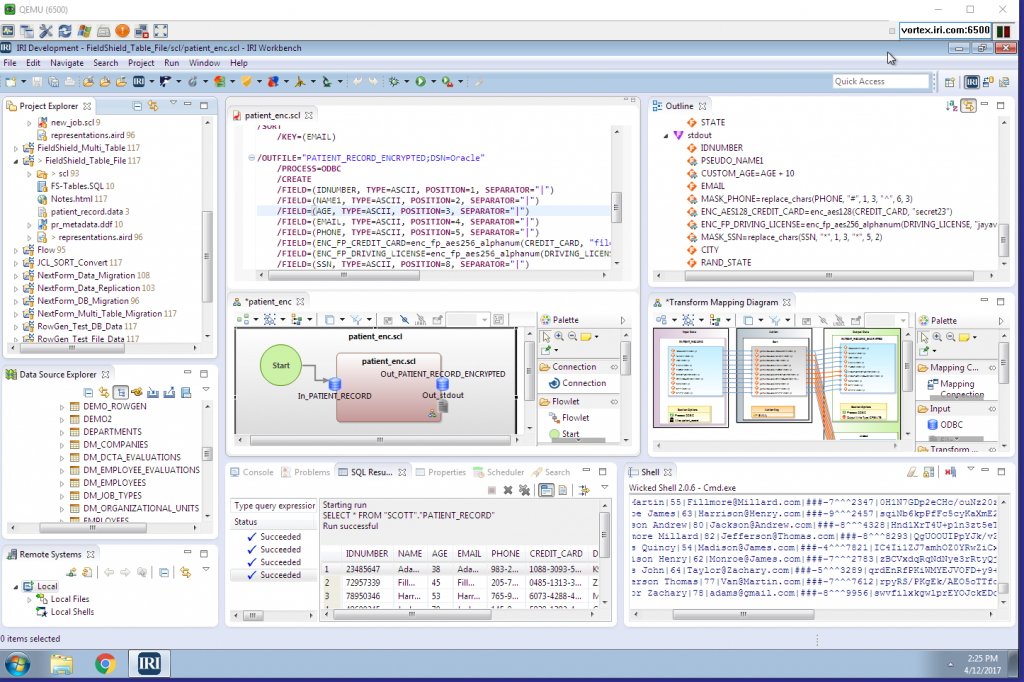
To demonstrate both static and dynamic data masking, we used IRI Workbench, the free graphical front-end for FieldShield and other IRI software, built on Eclipse™. In data security, compliance, and test data scenarios, Workbench users connect to their sources, perform discovery and classification, and then build and run static data masking functions.
More specifically, they define their data classes and search criteria, then apply consistent masking rules to protect it. This helps them govern their data better, and preserve the referential integrity of their sources. And it helps them conform with data privacy laws and business needs.
Workbench also supports re-ID risk scoring, database subsetting, test data generation and population, and many other data management capabilities enabled in the IRI Voracity platform, which includes FieldShield.
Being in Eclipse also means Workbench supports Java application development, and thus your programs that can dynamically mask or unmask data using library functions compatible with the static functions. Again, the API is documented in the FieldShield SDK.
This article provides a quick example of using FieldShield in Workbench for static data masking of a database table, and then unmasking that data dynamically in a Java program. Everything is configured in IRI Workbench.
Setting Up
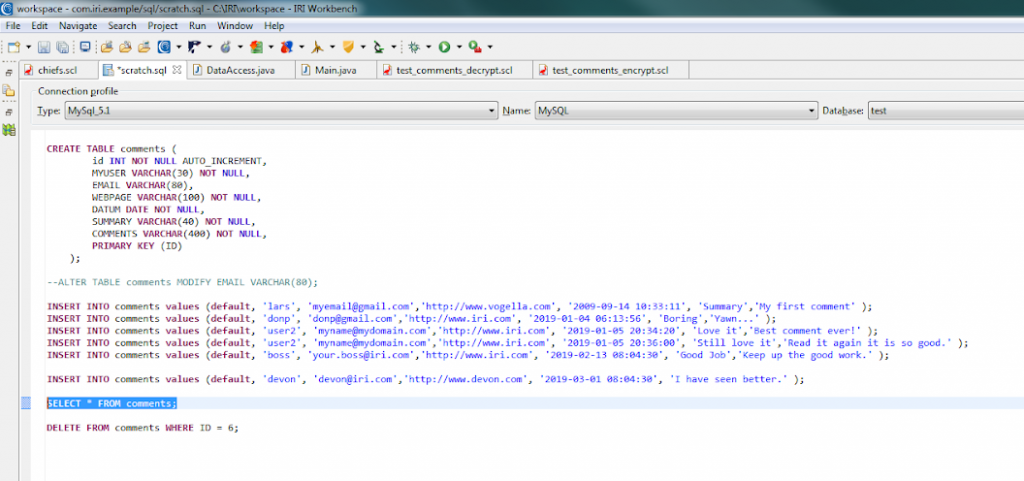
First, we built and populated a sample table in MySQL using the SQL scrapbook of the Data Tools Platform (DTP) plug-in. We defined columns for: username, email, time, and comments:
Static Data Masking
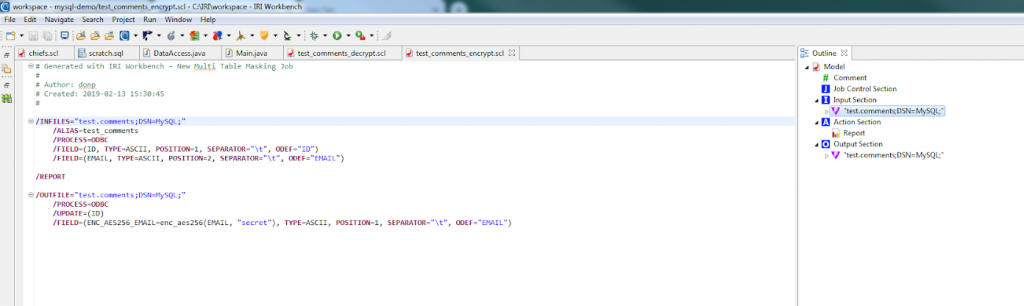
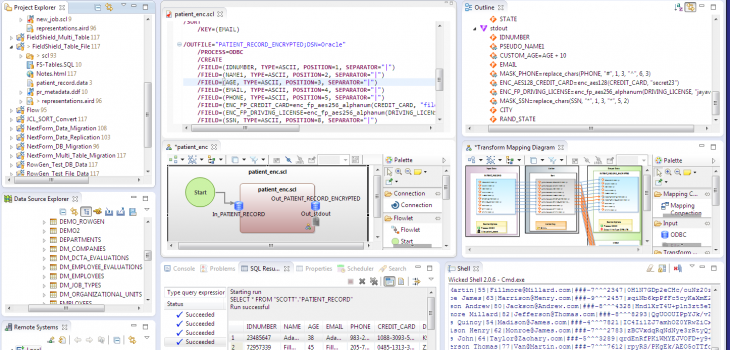
We used the ‘New Data Masking Job …’ wizard from the top toolbar menu in Workbench to quickly acquire that table and its metadata, and build a job to statically mask the email column using one of the AES 256 encryption functions in FieldShield, enc_aes256. In the FieldShield script that the wizard created, we can see the function to be applied to the column once, and then on new rows in the table when the same job is triggered or scheduled to run again.
Once run, the table in the MySQL database will have the email column encrypted.
Dynamic Data (Un) Masking
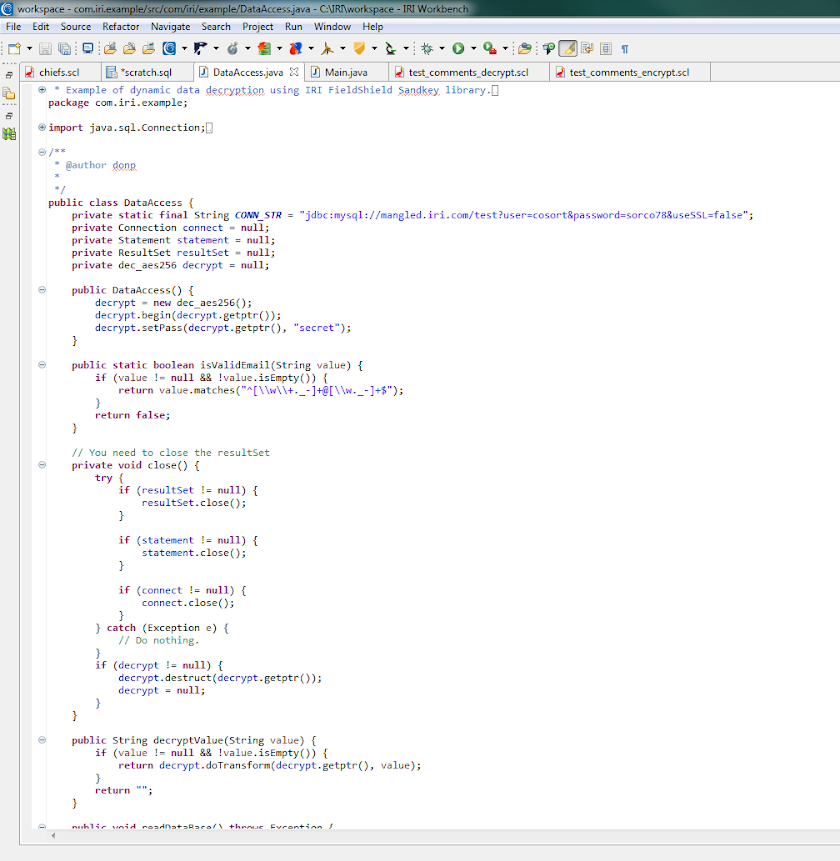
To demonstrate dynamic data unmasking, or decryption in this case, we called the corresponding decryption function, dec_aes256, in the FieldShield API library for Java:
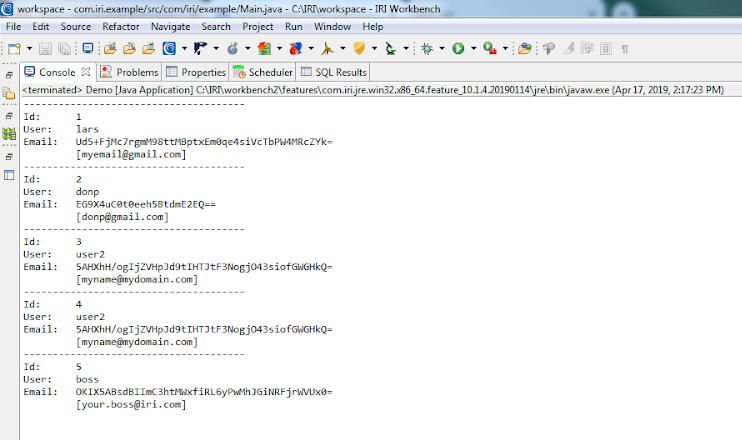
Similar calls are possible from .NET languages. This basic app shows how to connect to the MySQL table, validate the user, and display both the statically encrypted ciphertext value from the table, and the dynamically decrypted original plaintext email value in the console:
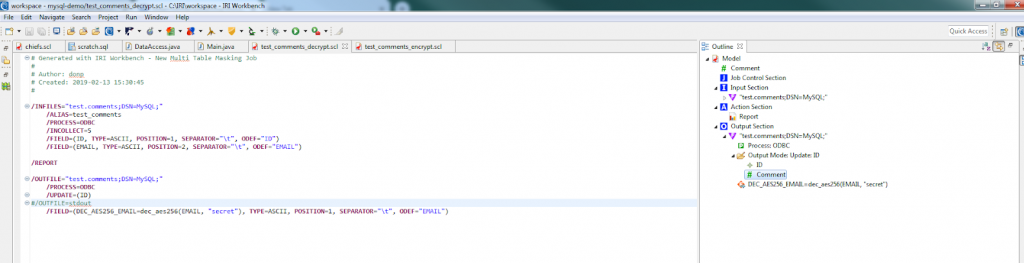
Of course, you also could have performed the decryption back in Workbench in static fashion with a similar, standalone FieldShield task like this:
The script above decrypts the ciphertext email values back to their original plaintext in each row of the database. The output can be the source table itself (to restore it), other targets (say, for testing), or both.1 Multiple tasks scripts addressing the masking or unmasking of multiple tables can be created automatically via FieldShield wizards in Workbench (and preserve referential integrity) with or without defined data classes.
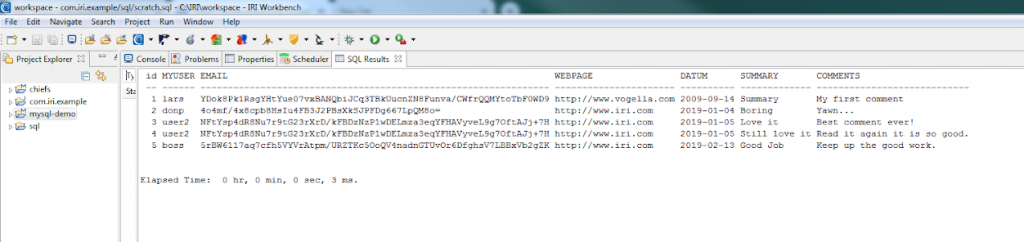
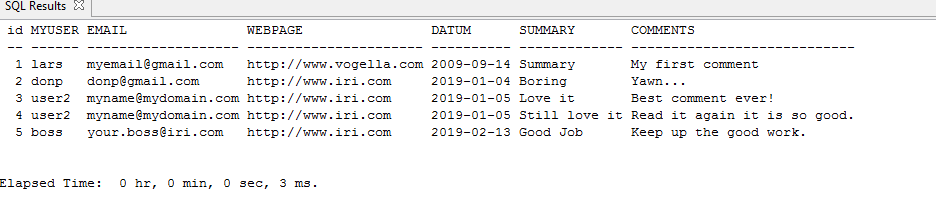
In this case, you can check that the values have been decrypted to their original form by connecting to your MySQL database and selecting the fields that you want to see, or by simply displaying the table in Workbench. The decrypted view is the original table:
The bottom line is that you can mask and unmask data statically or dynamically using IRI FieldShield. Use standalone mode for static operations, and API mode for dynamic. The masking functions are compatible, and every solution is enabled in the same pane of glass.
- More un/masking functions, plus many other transformation and reformatting functions (via an IRI CoSort or Voracity license), can run against that data in the same job script and I/O pass.