 Data Masking/Protection
Data Masking/Protection
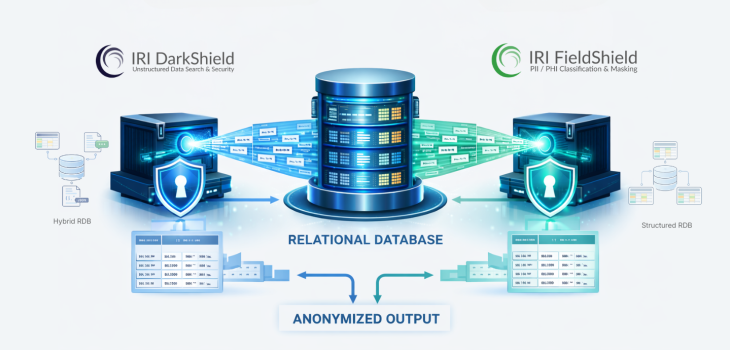
FieldShield vs. DarkShield for RDB Masking
The IRI Voracity Data Management platform and the IRI Data Protector suite provide robust data masking tools for finding and anonymizing sensitive data in different environments. Read More








