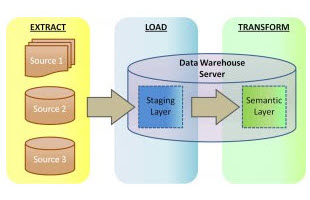
ETL vs ELT: We Posit, You Judge
Full disclosure: As this article is authored by an ETL-centric company with its strong suit in manipulating big data outside of databases, what follows will not seem objective to many. Read More
Full disclosure: As this article is authored by an ETL-centric company with its strong suit in manipulating big data outside of databases, what follows will not seem objective to many. Read More

Abstract: This article explains a method of protecting credit card data with tokenization using the IRI FieldShield data masking tool.
Submitting one’s credit card details electronically can be disconcerting (e.g., Read More

Note: This article was originally drafted in 2015, but was updated in 2019 to reflect new integration between IRI Voracity and Knime (for Konstanz Information Miner), now the most powerful open source data mining platform available. Read More
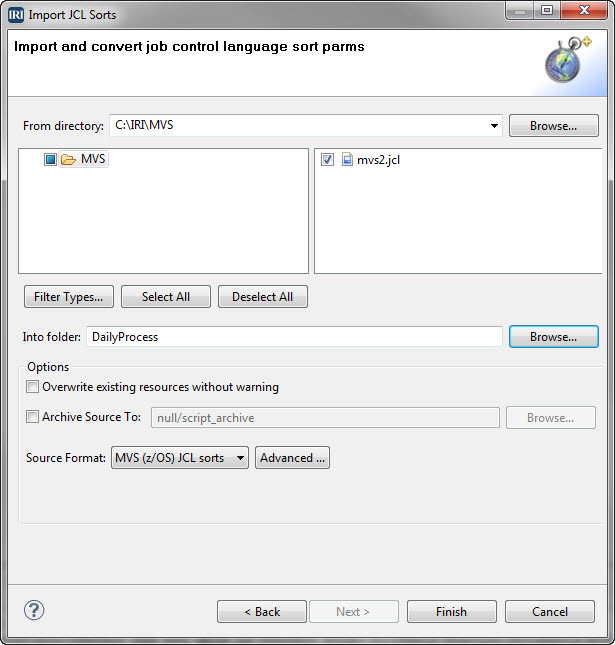
MVS, short for Multiple Virtual Storage, is the original operating system for IBM mainframe computers that is now z/OS. Its shell scripting or job control language (JCL), instructs the system how to run batch jobs or start subsystems. Read More
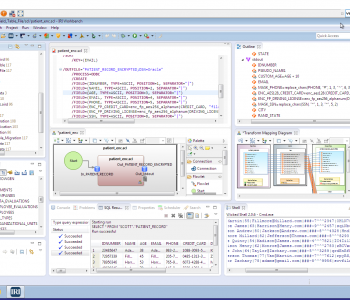
IRI Workbench is a powerful, and free integrated development environment (IDE) built on Eclipse designed for the user-friendly creation, management, and deployment of jobs in most IRI software products. Read More

Data Management and Protection Expertise – IRI Professional Services Now Open
In response to customer requests for bespoke applications across a broad range of data processing requirements, IRI now has an in-house business unit for the implementation of custom data transformation, ad hoc reporting, and data security solutions. Read More
Encryption key management is one of the most important “basics” for an organization dealing with security and privacy protection. Major data losses and regulatory compliance requirements have prompted a dramatic increase in the use of encryption within corporate data centers. Read More

Eclipse was originally started by IBM in the late 1990s in response to the need for a common development platform for all IBM products. Read More

This article deals with pseudonymization as one method of de-identifying or anonymizing sensitive data. IRI publishes more in-depth information on the topic in its learning center article on pseudonymization here. Read More

It is a common mistake to refer to data masking and data encryption interchangeably to mean the same things. While field-level encryption is considered one of many possible “data masking” functions, we define data masking and encryption as technically distinct processes below. Read More