Quick Links
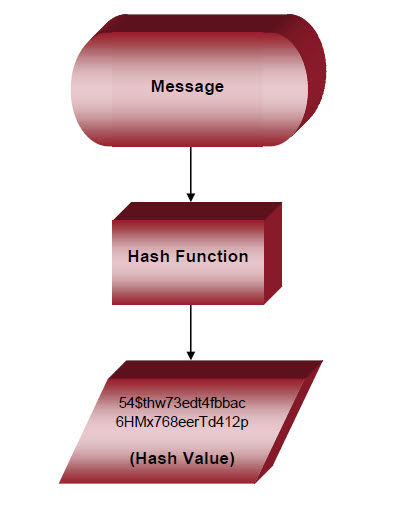
Hashing is a difficult-to-reverse data masking technique that converts a variable length "message" (e.g., someone's password) into an obfuscated, fixed-length, alphanumeric string. The message digest, or "hash value," can be an indexed look-up for the message. Sometimes there is more than one message per index (a "collision").
Because hashing is not as strong as encryption, or as reliably reversible, it is sometimes suitable for masking alone. More commonly, however, hashing is used with encryption. IRI supplies MD5, SHA1 and SHA2 hashing algorithms along with several encryption functions.
Hash functions are also used to generate checksums or Message Authentication Codes (MAC). These are created and sent along with messages like emails, EFTs, or passwords. When the message is received, its contents are run through the same hash function to create a new MAC. If the original and new MACs match, the message is authentic; if they do not, the message is likely to have been altered, and thus compromised.
Use the field-level hashing functions in the FieldShield, DarkShield or CellShield data masking tools in the IRI Data Protector suite, CoSort in the IRI Data Manager suite, or the IRI Voracity platform (which includes all of them) to help protect PII.
Or, create a MAC for one or more column values in each row. Include the MACs as an additional field or provide them in a separate file. Use the MAC to verify that the data in the record was undisturbed.
For more information and another use of hash values, see:
http://www.iri.com/blog/data-protection/hashing-tables-encryption/