Payment Card Security Challenges
Per every Experian industry forecast in the last five years, the number of data breaches will continue to rise. Ponemon Institute studies of data breaches reveal that the average cost to a US organization exceeds $200 for each compromised customer record.
With an average of 29,000 records compromised per incident, the cost of a data breach in this country can reach well over $5 million. In 2023 alone, the global average was $4.45M per breach, according the same Ponemon study IBM annually comissions.
In addition to the significant financial harm that results from a data breach, there is an acute loss of trust between an organization and its customers. Both the breach and the fallout are usually well publicized and long remembered.
And although the most expensive data breaches are in the healthcare sector, protecting payment card information is still a major issue because credit card numbers and account holder PII is routinely subject to hacks, theft, fraud and other misuse.
According to this SecurityMetrics analysis of Payment Card Industry (PCI) Data Breaches, despite the fact that 12 documented PCI 2.0 Data Security Standard (DSS) requirements were largely in place, external (50%), internal (33%) breaches still continued. The trend is worsening as the definitions of the 3.x and 4.x standard widens to include more forms of PII.
PCI DSS Compliance Solutions
To help mitigate or even nullify the effects of data breaches, and help BFSI companies and other organizations managing credit card data comply with PCI DSS requirements, the data discovery and masking functions in IRI Data Protector Suite products -- or the IRI Voracity platform -- find and protect primary account number (PAN), and other credit card number values (plus other data at risk) in multiple data sources.
These IRI data masking tools support PCI DSS rules for data-centric security through credit card data encryption, SHA-2 cryptographic hashing, and/or tokenization functions.
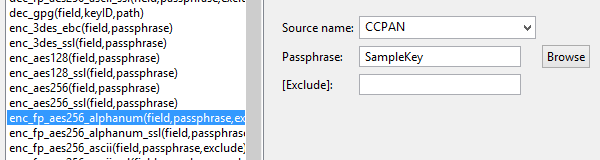
For example in structured data sources like normal form relational database columns and fields in flat files, IRI FieldShield users apply their choice of data classification, search methods, and data-centric security functions to PANs and other sensitive data in an intuitive, efficient, and flexible manner under Eclipse. For example, specification of an encryption cipher with a pass-phrase occurs in a simple dialog:
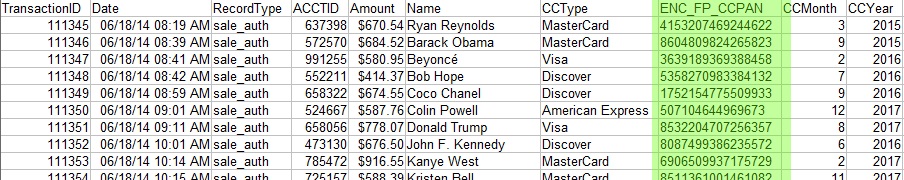
Here, format-preserving encryption is used for PCI DSS compliance, and to ensure that no changes are required to the table or database structure. Keeping the original look and feel to the values can also sometimes deceive hackers into thinking they have actual PANs.
These easy, yet powerful static data masking functions can also help you limit the financial and operational impact of a data breach. For example, Steam, a gaming distribution platform, suffered a data breach. As significant as the breach was, the overall impact to Steam was limited because the credit card values were encrypted.
FieldShield and the other IRI data masking tools (DarkShield for multiple forms of semi- and unstructured data, and CellShield for Excel spreadsheets) -- which share data classification, scanning, and data masking rules -- provide simplicity, affordability, and peace-of-mind by finding and securing credit card data and other PII at rest.
These proven data masking tools help organizations like this one meet PCI DSS requirements for protecting stored cardholder data, while mitigating the risk of data loss and providing safe, intelligent test data targets. In other words, data masking solutions for PANs have become recognized payment card security best practices.

It is also possible to encrypt/decrypt or redact PANs or PII in a dynamic data masking context, through an application that queries a database, for example. You can learn more about PCI DSS solutions in these top data masking tools through a live demo or free trial.
Blog Links